In the modern interconnected digital environment, cyber threats are changing at a pace none has ever been. Each and every application, mobile, web or API based, can serve as a point of attack. This is why small and big businesses are spending on effective application security testers to uncover the vulnerabilities in their software before they become a calamity.
Since the start ups through Fortune 500 companies, the need to have reliable and efficient security testing has soared. It is not a question of what to do with the application security testing tools anymore in 2026, as it is a potentially business-threatening decision to make. It is the complete guide that you should know about types and criteria to the top 10 tools that you should look into this year.
What Is Application Security Testing?
Application security testing refers to the procedure of examining computer software to determine vulnerabilities, weak spots and security defects, prior to their being taken advantage of by malicious entities. It is a complex of automated scan, manual analysis, and review of codes during the software development lifecycle (SDLC).
The objective is straightforward, identify and resolve the security vulnerabilities. You would largely mitigate the risk of data breach, compliance failures and costly security incidents, after the fact, by investing in application security testing tools as part of your development pipeline.
Types of Application Security Testing Tools
Static Application Security Testing (SAST)
SAST does not execute the application but examines the source code, binaries or bytecodes. It is white-box testing technique which assists a developer in identifying vulnerabilities within the coding stage of the development process, thus it is among the quickest techniques of discovering vulnerable code designs ahead of the code implementation.
Dynamic Application Security Testing (DAST)
DAST takes advantage of the testing and tests an application running by emulating real attacks externally. It is also referred to as black-box testing which identifies vulnerabilities found at runtime such as SQL injection, XSS, and authentication vulnerabilities in the system without the need to access the code.
Interactive Application Security Testing (IAST)
IAST switches between SAST and DAST agents: the agents are inserted into the application through runtime. It scans the app directly, offering real-time, very precise vulnerability scanning with low rates of false positive results – perfect in the current DevSecOps pipelines.
Mobile App Security Testing
Android and iOS vulnerabilities Mobile app security testing is aimed at detection of Android- and iOS-specific vulnerabilities. It analyses the permissions of the apps, data storage, network communication and reverse engineer threats to verify mobile applications against security standards.
API Security & Software Composition Analysis (SCA)
The API security testing is used to validate that APIs are not exposed to unauthorized access and data leakage. SCA patches the known vulnerabilities of the open-source components and third-party libraries to keep your software supply chain safe and compliant.
Criteria for Choosing App Security Testing Tools
There is a large variety of application security testing tools that can be hard to select. These are the main aspects to be taken into consideration:
- Coverage & Accuracy: Does the tool cover SAST, DAST, or IAST, or all three? Search for low false-positive rates.
- Integration Capabilities: Support compatibility with your CI/CD pipeline, IDEs, and DevOps workflows.
- User-Friendliness: A user-friendly interface and automatic scan make your team less hazardous to use.
- Scalability: The tool must be expanded as your application and team increase.
- Compliance Support: Find tools that comply with OWASP Top 10, PCI DSS, GDPR, and HIPAA.
- Expense & licensing: Trade off budget with feature requirements; numerous applications have free editions or open-source alternatives.
Best Application Security Testing Tools in 2026
| Sr No | Tool | Category | Best For | Free/Paid |
| 1 | MobSF | Mobile Security | Android & iOS Testing | Free (Open-Source) |
| 2 | Drozer | Mobile Security | Android Penetration Testing | Free (Open-Source) |
| 3 | Frida | Mobile Security | Dynamic Instrumentation | Free (Open-Source) |
| 4 | APKTool | Mobile Security | APK Reverse Engineering | Free (Open-Source) |
| 5 | Needle | Mobile Security | iOS App Security Testing | Free (Open-Source) |
| 6 | Burp Suite | Web App Security | Web Penetration Testing | Free & Paid |
| 7 | OWASP ZAP | Web App Security | DAST & Automation | Free (Open-Source) |
| 8 | Acunetix | Web App Security | Enterprise Web Scanning | Paid |
| 9 | Netsparker / Invicti | Web App Security | Proof-Based Scanning | Paid |
| 10 | Wapiti | Web App Security | Lightweight DAST | Free (Open-Source) |
10 Best Application Security Testing Tools List – 2026
A) Top Mobile App Security Testing Tools
1. MobSF (Mobile Security Framework)

MobSF is an effective, open-source mobile testing tool that is an all-in-one application security scanner. It can assist in the analytics of Android and iOS applications (static and dynamic). Her developers and security professionals find MobSF attractive due to the ability to scan automatically, its easy web-based dashboard and the possibility of analyzing APKs, IPAs and source code.
It can fit well into CI/CD pipelines, and therefore it is an option of choice when DevSecOps teams take mobile security testing into their early development lifecycle.
Key Features:
- Static & dynamic analysis
- REST API integration
- Malware detection engine
- Detailed security reports
Best For: Android & iOS automated security auditing
Website: https://mobsf.live/
2. Drozer
Drozer is a popular open-source security testing system, which has been developed to test Android applications. It enables security researchers and penetration testers to communicate with Android programs on a component level – testing activities, services and content providers.
Drozer has been the most relied on application security testing device in the mobile security environment and thus it is an all-encompassing analysis of the attack surface. It uses real world scenarios of attacks to reveal the latent vulnerabilities not realized by automated scanners in complex Android settings.
Key Features:
- Android component exploitation
- Attack surface analysis
- Module-based architecture
- IPC interaction testing
Best For: Android penetration testing & exploit simulation
Website: https://github.com/WithSecureLabs/drozer
3. Frida
Frida is a global open source dynamic instrumentation framework applied by computer security programmers to inject custom scripts into applications on the fly, be it a mobile phone or desktop computer. It works with Android, iOS, Windows, macOS, and Linux that is why it may be regarded as a truly multifunctional tool of any security tester.
Frida is one of the application security testing tools that are capable of hooking into the function calls, tracing the API behavior, and bypassing certificate pinning, in real time. It is the option of choice when reverse engineering and runtime manipulation of apps are needed at an advanced level.
Key Features:
- Runtime function hooking
- Cross-platform support
- SSL pinning bypass
- JavaScript-based scripting
Best For: Dynamic analysis & runtime manipulation
Website: https://frida.re
4. APKTool
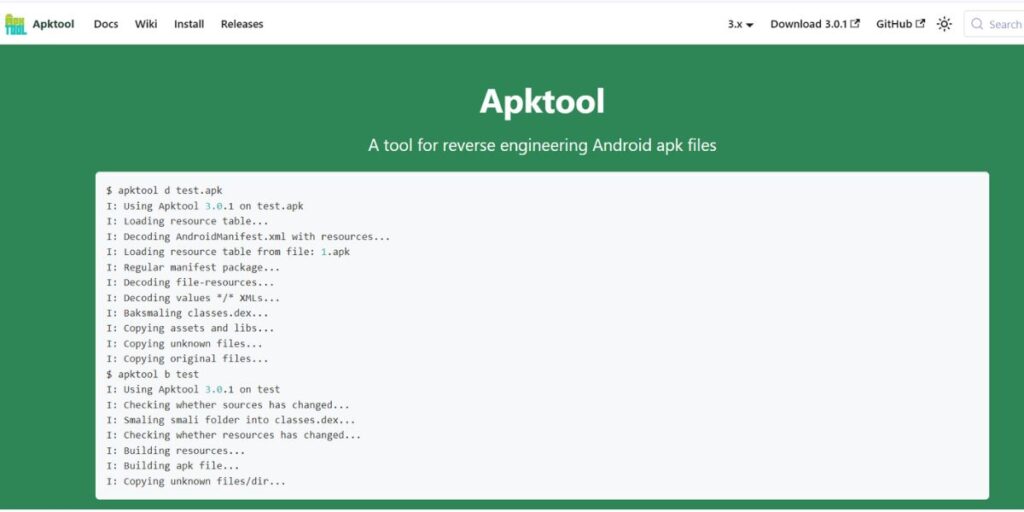
APKTool is a reverse engineering tool that is necessary to reverse engineer Android applications. It disassembles APK files into usable Somali code and resources so that security researchers can debug the obfuscated applications, retrieve the hard-coded secrets, and locate the latent vulnerabilities.
APKTool can be used as part of any mobile application security testing workflow to ensure that the workforce gets to know how a third-party application functions, and that their applications are not exchanging sensitive information. It is light in weight, a command-line-based application, and is frequently updated to accommodate the latest Android-based apps.
Key Features:
- APK decoding & rebuilding
- Smali code analysis
- Manifest file inspection
- Resource decompilation
Best For: Android APK reverse engineering
Website: https://ibotpeaches.github.io/Apktool
5. Needle
Needle is an open-source framework (iOS) security testing system created by MWR InfoSecurity. It makes it easy to perform security tests on iOS applications as it automates complicated tasks such as analysis of data storage, inspection of network traffic, and binary analysis.
Needle is one of the best tools in application security testing that can be used in teams operating with iOS. It can operate on jailbroken devices and it is modular so that the testers can execute specific modules based on the security concerns of the iOS application under test.
Key Features:
- iOS binary analysis
- Network traffic inspection
- Data storage assessment
- Modular testing framework
Best For: iOS app security assessments
Website: https://github.com/WithSecureLabs/needle
B) Best Web Application Security Testing Tools List
6. Burp Suite
Burp Suite by PortSwigger is the best in web application testing security. It is used by professional penetration testers all over the world and provides a vast set of tools to intercept web traffic, scan and test sophisticated authentication flows. The Community is a free edition, the Pro and Enterprise versions unlock advanced features and automatic scanning.
Burp Suite has been one of the most comprehensive application security testing tools in 2026 and provides unparalleled flexibility with the extensible environment of its plugins and a vibrant community of security practitioners.
Key Features:
- Proxy-based traffic interception
- Automated vulnerability scanner
- Burp Extender marketplace
- Intruder & Repeater tools
Best For: Professional web penetration testing
Website: https://portswigger.net/burp
7. OWASP ZAP (Zed Attack Proxy)
OWASP ZAP belongs to the category of the most popular and common free and open-source web application testing tools used to identify vulnerabilities. ZAP is trusted and maintained by the Open Web Application Security Project and is used by developers, testers, and security professionals worldwide.
It is compatible with active and passive scanning, automated testing through APIs and can be easily integrated with CI/CD pipelines. OWASP ZAP provides dependable and detailed performance regardless of whether you are a novice in the field of web security or a skilled user with automated scans in a DevSecOps set up.
Key Features:
- Active & passive scanning
- CI/CD pipeline integration
- REST API support
- Fuzzing & spider tools
Best For: Open-source DAST & DevSecOps automation
Website: https://www.zaproxy.org
8. Acunetix
Acunetix by Invicti is a high-end web vulnerability scanning tool that businesses rely on to be fast, accurate, and thorough. It applies the DeepScan technology to scan single-page apps that are heavy in JavaScript and identify more than 7,000 vulnerabilities, such as the OWASP Top 10 risks.
Being one of the leading commercial application testing tools in the area of application security, Acunetix can be readily integrated with issue tracking instruments like Jira or GitHub. Its user-friendly dashboard, risk prioritization, and compliance reporting features make it a popular choice among security teams of large-scale web application portfolios.
Key Features:
- DeepScan JavaScript crawling
- 7,000+ vulnerability checks
- AcuSensor IAST technology
- Compliance report generation
Best For: Enterprise-grade automated web scanning
Website: https://www.acunetix.com
9. Netsparker / Invicti
Invicti (previously Netsparker) is an effective enterprise web application security scanner that is characterized by its one of a kind proof based scanning technology. In comparison to other traditional scanners, which identify possible vulnerabilities, Invicti can ascertain exploitability and then alert, drastically limiting false positives. It is also one of the most precise application security testing instruments of huge organizations having hundreds of web resources.
Invicti has features of full automation, scheduling and team collaboration, which makes it perfect on security teams that require to scan thousands of applications within a short time without losing its accuracy.
Key Features:
- Proof-based vulnerability confirmation
- False-positive-free reporting
- API & web service scanning
- Team collaboration workflows
Best For: Large-scale enterprise web scanning
Website: https://www.invicti.com
10. Wapiti
Wapiti is an open-source and lightweight command-line web application vulnerability scanner with black-box testing, and does not need to have access to source code. It operates on a webpage crawling basis, inserting attack payloads to identify well-known vulnerabilities, like SQL injection, XSS, file disclosure, and SSRF.
Wapiti provides good results with minimum configuration, making it a good choice of tools in the application security testing tools kit of teams with a low budget and no need to install any software. Mostly used by developers who prefer a fast and scriptable security scan as part of automatic pipelines.
Key Features:
- Black-box DAST scanning
- Multiple injection modules
- HTML & JSON reporting
- Cookie & auth support
Best For: Lightweight open-source DAST scanning
Website: https://wapiti.sourceforge.io
Application Security Testing Best Practices (Checklist)
- Space Left on Security: Introduce application security testing tools with the SDLC to uncover vulnerabilities early in the development, rather than after the fact.
- Take a Multi-layer Strategy: Use SAST, DAST and IAST to have total coverage of all phases within the application lifecycle.
- Automate in CI/CD Pipelines: Include automated security scans in each build and release pipe to make sure that nothing is released before it is checked.
- Periodically Revise Your Tools: Make sure that your security tools and your vulnerability databases are updated in order to identify the newest threats and zero-day exploits.
- Prioritize And Remediate Fast: primary vulnerabilities first: Risk based prioritization is used to remediate the most important vulnerabilities first, SLAs should be defined depending on the severity level.
- Educate Your Development Teams: It is the security of everyone. Train on secure coding practices and interpretation of findings of security tools on a periodic basis.
Conclusion
Application security is not a check box anymore, but a strategic requirement in 2026. As cyber threats continue to become increasingly advanced with each passing day, possessing the correct application security testing tools may be the only difference between a secure product and a crippling breach.
This list of the 10 best tools should have something that fits any team and any budgeted budget regardless of whether you are protecting a mobile app, a web platform, or a complex API ecosystem. Begin by evaluating your present security posture and identify vulnerabilities and select tools that will fit unobtrusively into your development process. Security begins with being aware of it – and the right tools are everything.
Explore More About:
FAQs
What are application security testing tools?
They are software platforms used to detect, analyze, and assist in repairing security weaknesses in applications – web, mobile, and API platforms at any development phase.
What should be the preferred tool of free application security testing in 2026?
The best free tools are OWASP ZAP and MobSF, which provide strong scanning abilities for web and mobile applications, respectively.
What is the distinction between SAST and DAST?
SAST is a source code analyzer (static) that does not execute the application, whereas DAST is a source code analyzer (dynamic) that executes a live, running application through simulating real-world attacks.
Is enterprise security testing equipment applicable to small businesses?
Yes – several of them such as Burp Suite Community Edition, the OWASP ZAP, and Wapiti are free of charge and can be used by small teams with limited funds.
What is the frequency of application security testing?
Ideally, security tests are to be automated with each commit of code into your CI/CD pipeline or each build, and periodic (such as monthly, or major release) wide scans.

